Subscriber Benefit
As a subscriber you can listen to articles at work, in the car, or while you work out. Subscribe NowThe military conflict involving Iran, Israel and the United States is happening thousands of miles from Indiana, but local cybersecurity experts say it can create impact much closer to home.
That, the experts say, is because international conflicts in the physical world can lead to a spike in cyberattacks — both on government entities and on private companies that don’t necessarily have any connection to the conflict itself.

“Anytime we see any kind of conflict between nations, cyber is definitely one of the battlefields,” said Cody Tyler, chief information security officer at Indianapolis-based Exos, an IT, cybersecurity and staffing firm.
It’s especially true for the current conflict, because “Iran has a quite long and storied history of supporting and financing and even being directly responsible for many [cyber] threat actor groups,” said Michael DeNapoli, senior solutions architect at Indianapolis-based cybersecurity firm Pondurance.
Within days of the start of the Iran conflict on Feb. 28, DeNapoli said, Pondurance began to see an increase in scanning traffic and hunting traffic — activities indicating that cyberattackers were stepping up their efforts to identify potential targets.
On March 11, Michigan-based medical-equipment manufacturer Stryker disclosed that it had been hit by a cyberattack that had created a “global network disruption” to its Microsoft systems. As of Monday, according to updates Stryker has posted on its website, the company was still working to restore its systems, including manufacturing activities.

The Stryker attack was especially significant, DeNapoli said, because the company makes such a wide range of products, from surgical instruments to stretchers, defibrillators, disinfectants and more.
“Almost every health care organization on this planet buys products from Stryker,” DeNapoli said.
Although Stryker’s online updates have not identified who is responsible for the cyberattack, a group called Handala Hack took credit for the incident. On March 19, the U.S. Department of Justice announced it had taken down four websites connected to Iran’s Ministry of Intelligence and Security — including the website where Handala Hack claimed credit.
DeNapoli said he also expects to see an increase in cyberthreat activity overall — not just activity coming from one of the countries directly involved in the conflict.
“We’ll definitely see other threat actors taking advantage of the situation — Iran essentially inadvertently offering them cover to perform their own threat activity,” DeNapoli said.
Increased activity
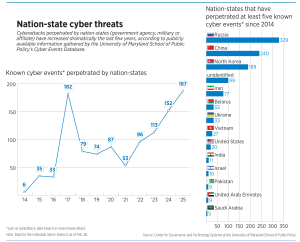
It can be difficult to determine exact numbers when it comes to cyberattacks because victims don’t always disclose such incidents.
But, DeNapoli said, cyberthreat activity has gone way up this year.
And since 2022, he said, cyberthreat activity has increased 100% to 200% each year. But organizations that track such activity indicate that attacks might be up as much as 400% so far this year over the same period last year.
“While not all of it can be tied back to Iranian threat actors, it is far and above the expected increase that we should have seen. And so we have to draw the conclusion that the conflict and the amount of threat activity coming from Iran is significantly ramped up,” DeNapoli said.
In a research brief issued March 12, S&P Global Ratings said the Middle East conflict “has materially increased geopolitical risk and could trigger a significant and prolonged period of cyberwarfare” that could affect the wider economy.
“Iran and its proxies have a history of targeting energy, defense, government, and municipal infrastructure, including transportation, industrial, health care, water utilities, finance, and education,” the S&P report said.
The report also noted that the United States and Israel have launched their own cyberattacks on Iran’s military and infrastructure.
After the Stryker attack became public, DeNapoli said, Pondurance fielded multiple calls from clients in health care and other industries who were worried about their own vulnerabilities.
Protective measures
Experts say organizations can take lots of steps, both high-tech and low-tech, to protect themselves against cyberthreats.
Tyler recommends that organizations protect their accounts with multifactor authentication — for instance, requiring that users enter both a password and a code sent to their smartphone before they can access an account. For users who have administrator-level access to accounts, Tyler recommends a stronger level of protection known as phishing-resistant multifactor authentication.

Carol Choksy, a senior lecturer at Indiana University’s Luddy School of Informatics, Computing and Engineering, recommends keeping up with new software patches — installing the latest updates and fixes that developers issue to address security problems or bugs.
She also recommends that executives step back and look at the bigger picture: Consider what information the organization has, which is most important to protect, how hackers might try to gain access to that information, and what is the best way to protect it. It’s also important to realize, she said, that no system is 100% foolproof.
“The bad guys, they’re inventive. They’re creative,” Choksy said.
Staff training is also paramount, DeNapoli said.
Many cyberattackers gain access to a network through phishing — contacting victims by email, text or phone calls to trick them into providing personal information.
Phishing perpetrators might claim to represent a government agency, a well-known company or the recipient’s boss as a way to convey a sense of authority, DeNapoli said. They might also ask the potential victim to do something specific like click on a link or call a specific number. And they might say this action needs to happen right away.
“The combination of all three together is a strong indicator that something is not right,” DeNapoli said.
Organizations should also adopt the stance that employees won’t be disciplined if they accidentally click on a suspicious link or make some other cybersecurity mistake — as long as they tell their IT department about it right away, DeNapoli said. If the mistake did create an opening for cybercriminals, it will become a much bigger problem if not dealt with promptly.
Tyler said it’s also important to have a response and recovery plan that includes elements like how critical systems will be isolated in case of a breach, who is responsible for doing what and how to recover after an incident. Creating immutable backups — backups that can’t be altered or deleted — is also an important step, Tyler said.
“You should assume [that] at some point you are going to have some type of breach,” he said.
It won’t stop

Steve Long, CEO of Hancock Health, knows that firsthand. The organization operates a hospital in Greenfield, a physician network with numerous clinics, and wellness centers in Greenfield, McCordsville and New Palestine.
Long said the Middle East conflict is leading to an increase in cyberthreats, but he added that hospitals are always a target — and usually by criminals looking for money.
“We are attacked every day. Every hospital is,” he said. “The bigger the place, the more times they’re attacked.”
Most of those attempted attacks are defeated, Long said, but cybercriminals have broken through twice in the 12 years he’s been CEO.
On one of those occasions, in 2018, Hancock Health was hit by a ransomware attack and paid the hackers a ransom of four Bitcoin, about $55,000 at that time, to regain access to its system.
“We learned a lot from that,” Long said.
Since then, he said, the hospital has beefed up its cybersecurity infrastructure and staff training, including implementing multifactor authentication for all accounts, using both artificial intelligence and humans to monitor the system’s networks 24 hours a day, and increasing the amount of cybersecurity training employees receive.
It’s unclear when the conflict with Iran will end, but DeNapoli said organizations should remain vigilant even after the current hostilities cease.
“Right now, it’s Iran, and it’s undeniable that it is Iran that is performing a lot of these, this uptick in attacks,” DeNapoli said. “But there will always be someone trying to breach an organization or a doctor’s office or manufacturing plant or a government entity. It will always be happening. And so we as a business community, as government communities, need to start defending ourselves better.”•
Please enable JavaScript to view this content.